Some services run really good behind a reverse proxy on 443, but some others can really become an hassle… And sometimes just opening other ports would be easier than to try configuring everything to work through 443.
An example that comes to my mind is SSH, yeah you can use SSLH to forward requests coming from 443 to 22, but it’s so much easier to just leave 22 open…
Now, for SSH, if you have certificate authentication or a strong password, I think you can feel quite safe, but what about other random ports? What risks I’m exposing my server to if I open some of them when needed for a service? Is the effort of trying to pass everything through 443/80 worth it?

With SSH it is easier to do key authentication. Certificate authentication is supported but it is a little more hassle. Don’t use password authentication as it is deprecated and not secure.
The key with SSH (openssh specifically) is that it is heavily audited so it is unlikely to have any issues. The problem is when you start exposing self hosted services with lots of attack surface. You need to be very careful when exposing services as web services are very hard to secure and can be the source of a compromise that you may or may not be aware of.
It is much safer to use a overlay VPN or some other frontend for authentication like mTLS or an authenticated reverse proxy.
Be sure to keep everything up to date too. Even openssh has had multiple vulnerabilities just this year.
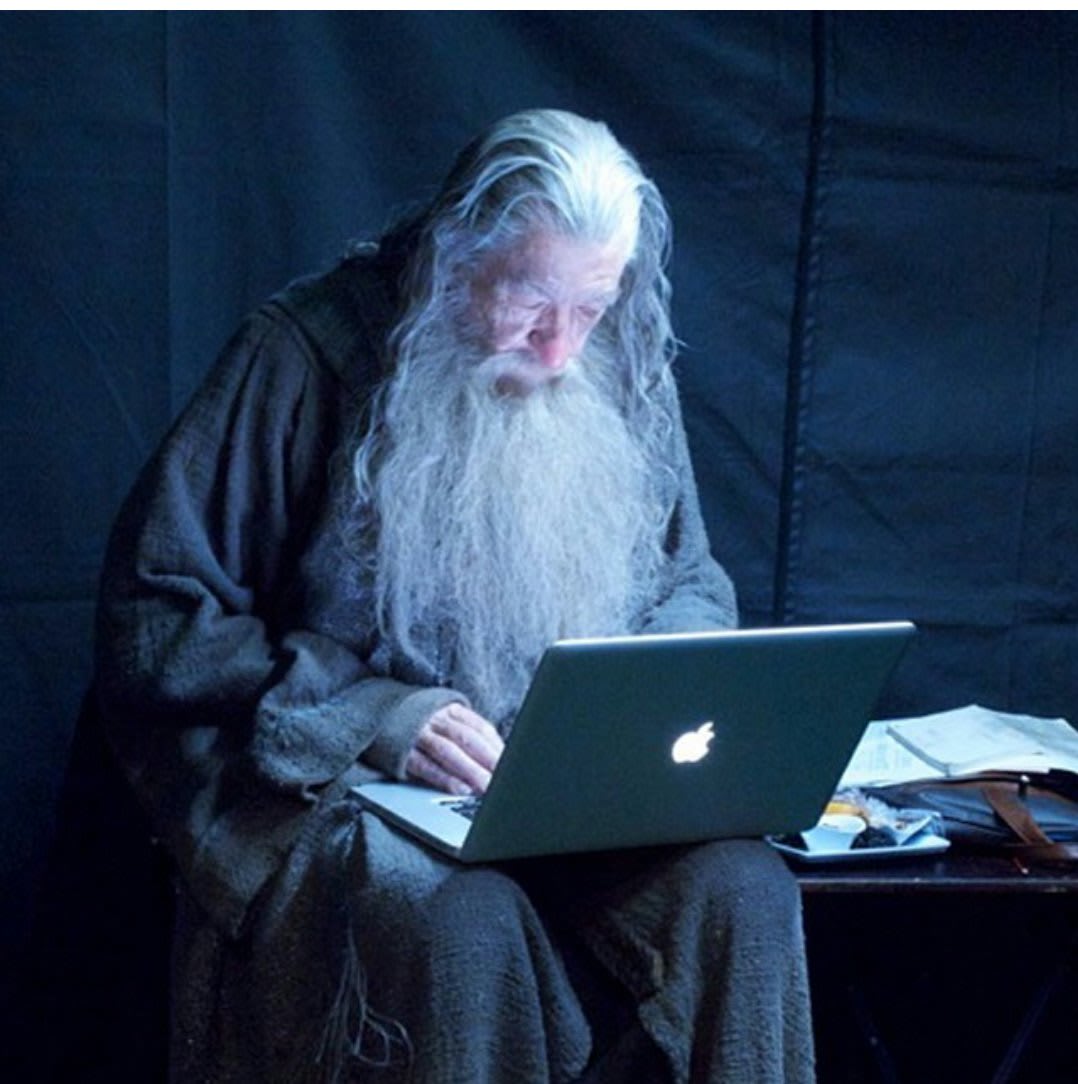
Always good advise
However, OpenSSH is pretty solid security wise. https://www.openssh.com/security.html
Note: it is best to check the official security pages instead of random websites.
Vendors packaging OpenSSH open up even more vulnerabilities that the devs of OpenSSH can’t protect you from. See the recent xz poisoned OpenSSH packages